Most freight fraud conversations focus on external threats.Fake carriers. Identity theft. Double brokering. But sometimes, the biggest risk is not outside your operation, it’s sitting inside it.
A recent fraud case involving over $800,000 in fake freight jobs revealed something uncomfortable but important: the system didn’t fail because it was hacked. It failed because no one was checking the process.
For freight brokers, this isn’t just a story, it’s a warning.
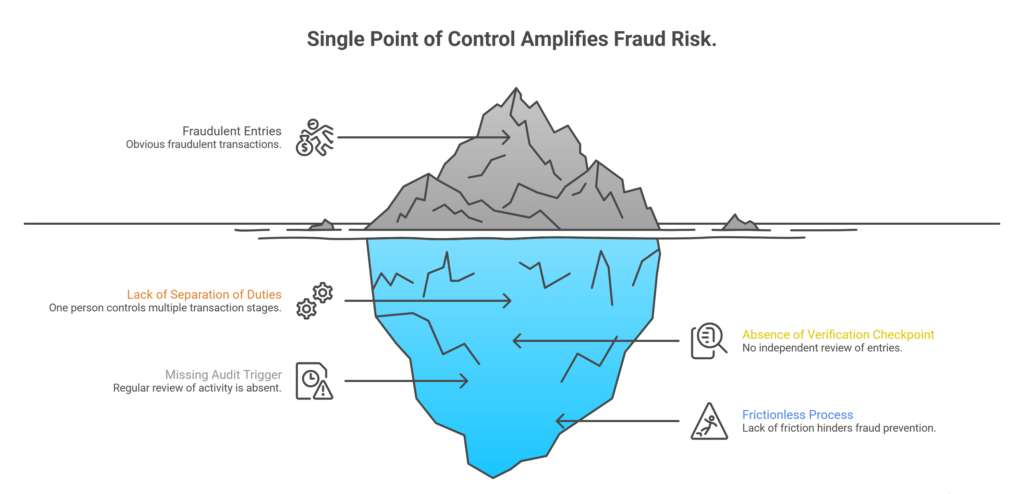
When One Person Controls Everything, Risk Multiplies Fast
In this case, the fraud wasn’t complex. It didn’t require advanced technology or sophisticated schemes. It relied on a simple breakdown: one individual controlled both contract approvals and carrier assignments.
In our experience, this type of operational overlap creates one of the highest-risk environments in freight brokerage.
Here’s why:
- No separation of duties: When the same person manages multiple stages of a transaction, there is no built-in accountability (Transportation Intermediaries Association [TIA], n.d.)
- No verification checkpoint: Without independent review, fraudulent entries can move through the system unchecked
- No audit trigger: If no one is reviewing activity regularly, patterns go unnoticed
- No friction in the process: And in fraud prevention, friction is often a good thing
Think of it this way: if your process is too smooth, it might also be too easy to manipulate.
In our experience, the most secure brokerages intentionally build controlled friction into their workflows such as extra steps that force validation before execution.
“The biggest risk isn’t complexity, it’s simplicity without oversight. When processes lack checkpoints, fraud doesn’t need to be sophisticated to succeed.”
Where in your workflow does one person currently have too much control without oversight?
Fake Freight Doesn’t Require Fake Trucks, Just Weak Controls
One of the most surprising aspects of this case is that no freight actually moved.
The fraud was entirely administrative. Contracts were created, payments were processed, and everything appeared legitimate, on paper.
In our experience, this type of fraud highlights a critical misconception: You don’t need stolen trucks or fake carriers to lose money. You just need weak internal validation.
Common vulnerabilities that allow this include:
- Lack of carrier verification beyond initial onboarding (TIA, n.d.)
- No cross-check between load confirmation and actual shipment movement
- Missing proof-of-delivery validation processes
- Automated payments without multi-step approval workflows
For example, if a brokerage processes payments based solely on internal records without verifying shipment completion, it creates an opening for false billing.
Fraud doesn’t always break the system. Sometimes, it just quietly uses it.
“Fraud rarely starts with a major failure, it starts with small assumptions that go unverified.”
How many layers of validation exist between booking a load and releasing payment in your operation?
Case Study Breakdown: How the Scheme Went Undetected for Years
Let’s break this down from an operational perspective.
Initial Setup:
- A single employee had authority over both carrier assignment and contract approval
- A second party acted as the “carrier” receiving payments
- No independent verification was required between these steps
What Happened Over Time:
- Fake freight jobs were created and processed
- Payments were issued for loads that never existed
- A portion of the funds was redirected internally
Why It Wasn’t Caught:
- No audit system reviewing transaction patterns
- No requirement to verify shipment completion externally
- No separation between financial approval and operational execution
Estimated Impact:
- Over $800,000 in losses across approximately three years
- Consistent activity that blended into normal operations
In our experience, long-term fraud schemes are rarely hidden, they’re simply not reviewed.
If no one is looking for inconsistencies, even repeated patterns can appear normal.
After implementing basic controls, such as separating responsibilities and auditing payment flows, this type of scheme becomes significantly harder to execute.
“Fraud doesn’t need to be invisible, it just needs to be ignored.”
If someone reviewed your last 90 days of transactions, what patterns would stand out?
Vetting Isn’t Just for Carriers, It’s for Processes and People Too
When brokers think about vetting, they usually think about carriers.
Insurance checks. Authority validation. Safety scores.
But this case shows that vetting must go beyond external partners. It must include internal processes and roles.
In our experience, strong brokerages apply vetting principles to:
- Employee responsibilities: Defining clear boundaries between roles
- Process ownership: Ensuring no single individual controls an entire workflow
- Approval systems: Requiring multiple checkpoints before financial actions
- Ongoing audits: Regularly reviewing transactions and operational patterns
For example, separating load booking, carrier approval, and payment authorization into different roles can significantly reduce risk.
It’s not about distrust, it’s about structure.
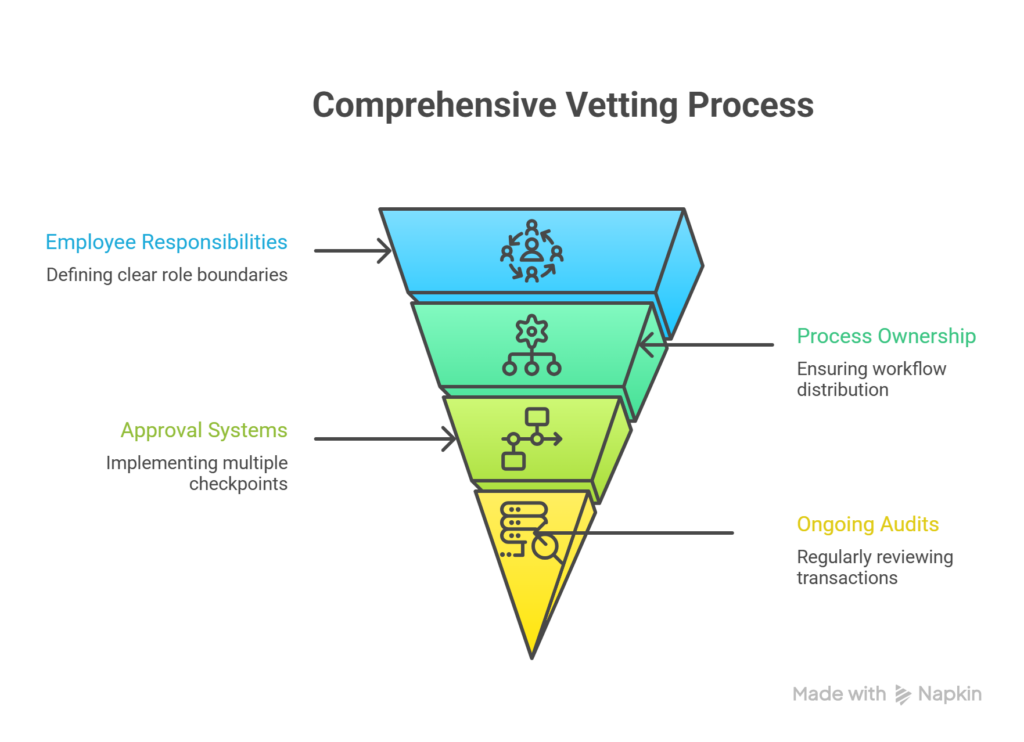
“Vetting is not a one-time action, it’s a system of continuous verification across people, processes, and transactions.”
Are your payment and vetting processes built to catch issues before they cost you? See how stronger controls can protect your cash flow.
Technology Helps, But Only If Paired With Process Discipline
Technology is often seen as the solution to fraud. And it helps, especially with tracking, verification, and automation.
But in our experience, technology without process discipline is like installing security cameras and never checking the footage.
Effective fraud prevention combines:
- TMS-based workflow controls: Restricting who can approve, assign, and process loads (DAT Freight & Analytics, n.d.)
- Automated audit logs: Tracking changes and approvals across the system
- Document verification tools: Ensuring consistency across rate confirmations, invoices, and PODs
- Exception alerts: Flagging unusual patterns or repeated transactions
For example, if a system flags repeated payments to a single carrier without corresponding delivery confirmations, that’s a signal worth investigating.
Technology doesn’t replace oversight, it enhances it.
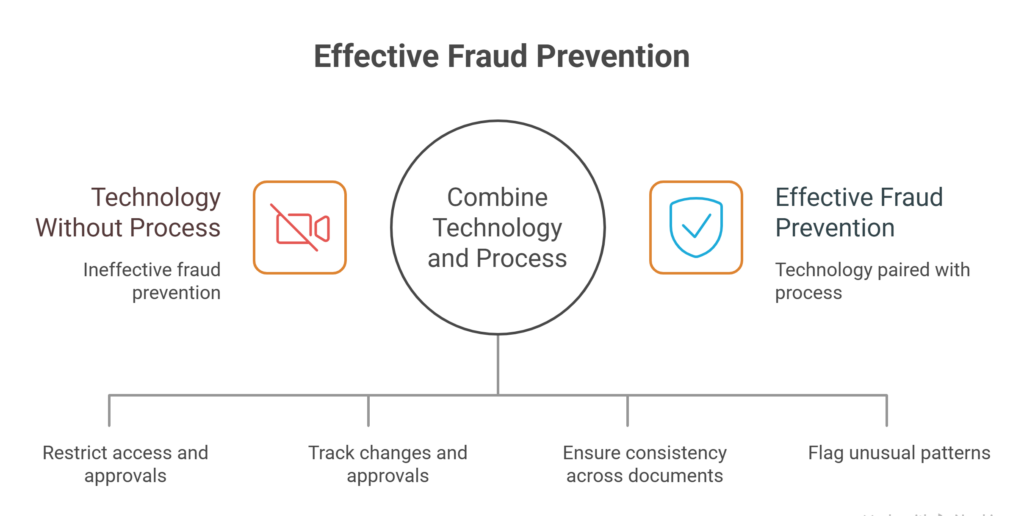
“The strongest systems don’t just process transactions, they question them.”
Is your technology helping you detect fraud or just process it faster? Discover tools that add real visibility and control to your operations.
The Real Takeaway: Fraud Prevention Is an Operational Strategy
This case isn’t just about fraud, it’s about how operations are structured.
The loss didn’t happen because the company lacked tools. It happened because the system allowed too much control without verification.
In our experience, brokerages that treat fraud prevention as part of daily operations, not just a compliance task, are far more resilient.
This includes:
- Designing workflows with built-in checks
- Training teams to recognize red flags
- Regularly auditing financial and operational data
- Continuously improving processes based on real-world risks
Because at the end of the day, fraud doesn’t exploit systems, it exploits gaps.
And those gaps are often preventable.
“Fraud prevention isn’t a reaction, it’s a design choice built into your operation.”
If you were designing your brokerage from scratch today, what controls would you build in from day one?
Frequently Asked Questions (FAQs)
1.How can freight brokers prevent internal fraud?
By implementing separation of duties, requiring multi-step approvals, conducting regular audits, and using technology to track and verify transactions.
2.Is the carrier vetting enough to prevent fraud?
No. While carrier vetting is essential, internal process controls and employee role separation are equally important in preventing fraud.
3.What is the biggest red flag in freight fraud cases?
One of the biggest red flags is when a single individual has control over multiple stages of a transaction without oversight or verification.
Build Systems That Prevent Freight Fraud
Freight fraud doesn’t always come from external threats. Sometimes, it develops quietly within systems that were never designed to question themselves.
The $800K+ scheme we examined didn’t rely on sophisticated tactics, it relied on unchecked control, missing verification, and a lack of oversight.
For freight brokers, the takeaway is clear: vetting isn’t just about who you work with, it’s about how your entire operation is structured.
The brokerages that succeed today won’t just move freight efficiently, they’ll build systems that verify, validate, and challenge every step of the process. Because in freight, what you don’t check can cost you.
Ready to strengthen your internal controls and prevent costly fraud? Contact us to learn how our Freight Broker Solutions can help you build smarter, more secure operations.
References
FreightCaviar. (2026). Freight fraud case insights and industry news.
https://www.freightcaviar.com
Transportation Intermediaries Association (TIA). (n.d.). Fraud prevention and carrier vetting best practices.
https://www.tianet.org
DAT Freight & Analytics. (n.d.). Freight technology and workflow systems.
https://www.dat.com




